Services
- Cloud Enablement Data & AI Digitalization End-to-End Digital Marketing SaaS
Industries
Products
- Retail Healthcare Hospitality Insurance Productivity Technology Marketing
Resources
Company
Cloud Enablement
Cloud Consulting
Cloud-Native Apps
Cloud Migration Strategies
Cloud Migration Services
Cloud Monitoring
Cloud Security Posture
AWS
Cloud Cost Optimization
Azure
GCP
App Engine
Private Cloud
Data & AI
Overview
Generative AI Development
Data Science
AI Agents
Data Engineering
Artificial Intelligence
Data Management
Machine Learning
Data Storage
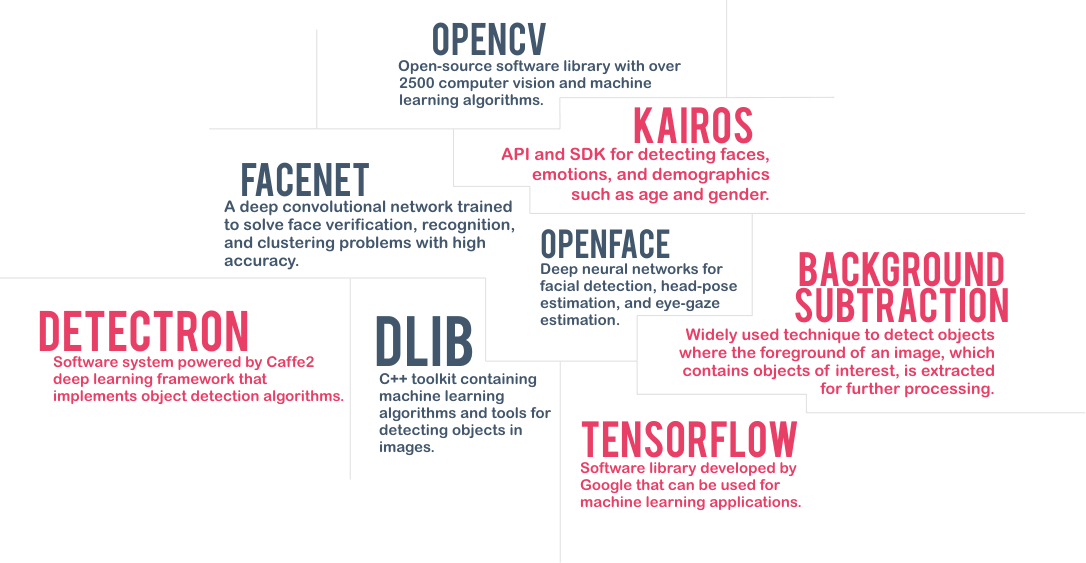
Computer Vision
Data Visualization
Video Analytics
Digitalization
Mobility
Extended Reality
Web Development
Internet of Things
Blockchain
CRM
RTLS
RPA
E-Learning Portals
E-Commerce Sites
Intelligent Document Processing
Product Information Management
Enterprise Asset Management
Digital Experience Platform
Customer Data Platform
Enterprise Resource Planning
End-to-End
Site Reliability Engineering
UX Design
Microservice Architecture
QA Automation
DevOps
Performance Monitoring
Cybersecurity
Frontend Monitoring
API Management
Compliance Consulting
Digital Marketing
Overview
Marketing Automation
Visualization
Analytics
Programmatic Advertising
Paid Advertising
SEO
Email Marketing
Content Marketing
Social Media
Hospitality
TalQCall accounting system
Insurance
RehashLow-code insurance platform
Productivity
AsQAI employee assistant
Notification AppNotification builder
KeverProject management tool
QuickPicksSalesforce widget
Marketing
PartnerFrontAffiliate marketing platform